EDR is not AV
Please stop conflating the terms
Sure, they’re often bundled together and sold together.
But EDR is not AV.
Welcome to the first edition (in this new Substack, at least) of Adrian thinks someone is wrong on the Internet and will bang on a keyboard well past midnight to make his point.
What’s the difference?
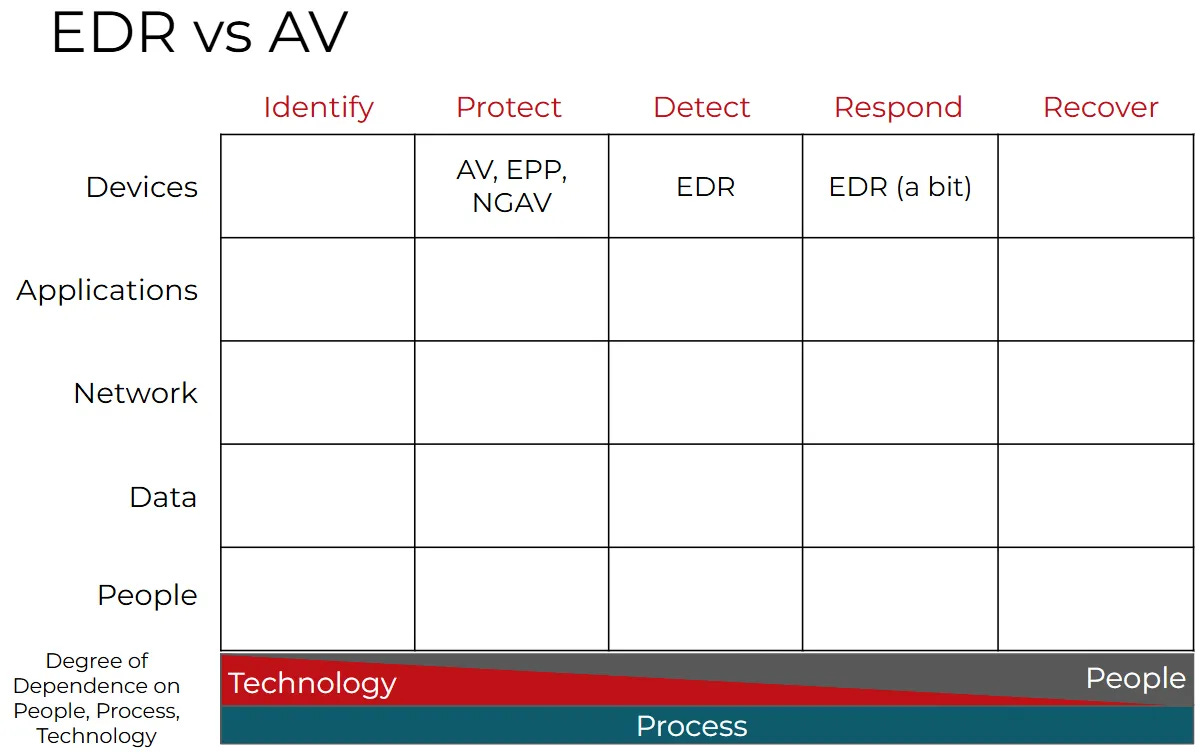
EDR is not AV. Nor did EDR replace AV. They are very different technologies that serve different use cases. Endpoint Detection and Response gathers endpoint telemetry: file, process, and network activity. This data is fed to an event monitoring (e.g. XDR or SIEM) system. It is then manually (SOC analysts, threat hunting) or automatically (SOAR playbooks, AI) acted upon, after something bad has happened. EDR can take some automated actions, but the options are typically very limited (more on that in a few paragraphs).
Unlike EDR, Antivirus (aka NGAV, aka anti-malware, aka etc) attempts to prevent malware and other attacks from infecting or impacting systems. It aims to do this job without human intervention, at machine speed. Adding to the acronym salad, EPP (endpoint protection platform) is antivirus plus other adjacent endpoint security technologies, like device control, disk encryption, host firewall/IPS, application control, and many other potential features that vary from vendor to vendor.
In NIST Cybersecurity Framework terms, AV belongs in the “protect” column, while EDR mostly sits in the detect column, with some rudimentary response capabilities (isolate machine from network, etc) that technically put it in the ‘response’ column as well. Protect is left of boom - it aims to prevent the boom. ‘Boom’ is an undesirable event that security teams want to prevent: denial of service, exploitation, malware infection - some compromise or loss of control. EDR is right of boom, it collects information after the bad thing has happened, giving security operations and incident response teams a starting point for detecting, containing and eradicating the threat.
Why are they separate?
There are many scenarios where AV may be necessary or required, but where systems can’t handle running AV and EDR. For example, I don’t expect to find 15 year old point-of-sale hardware running Crowdstrike’s full enterprise NGAV+EDR enterprise Falcon client. Or perhaps the environment is so locked down that EDR is deemed unnecessary. I could also think of situations where AV is unnecessary (either because it’s already built in, or the system is so locked down, it can’t function), but you do want to collect forensic data from the device.
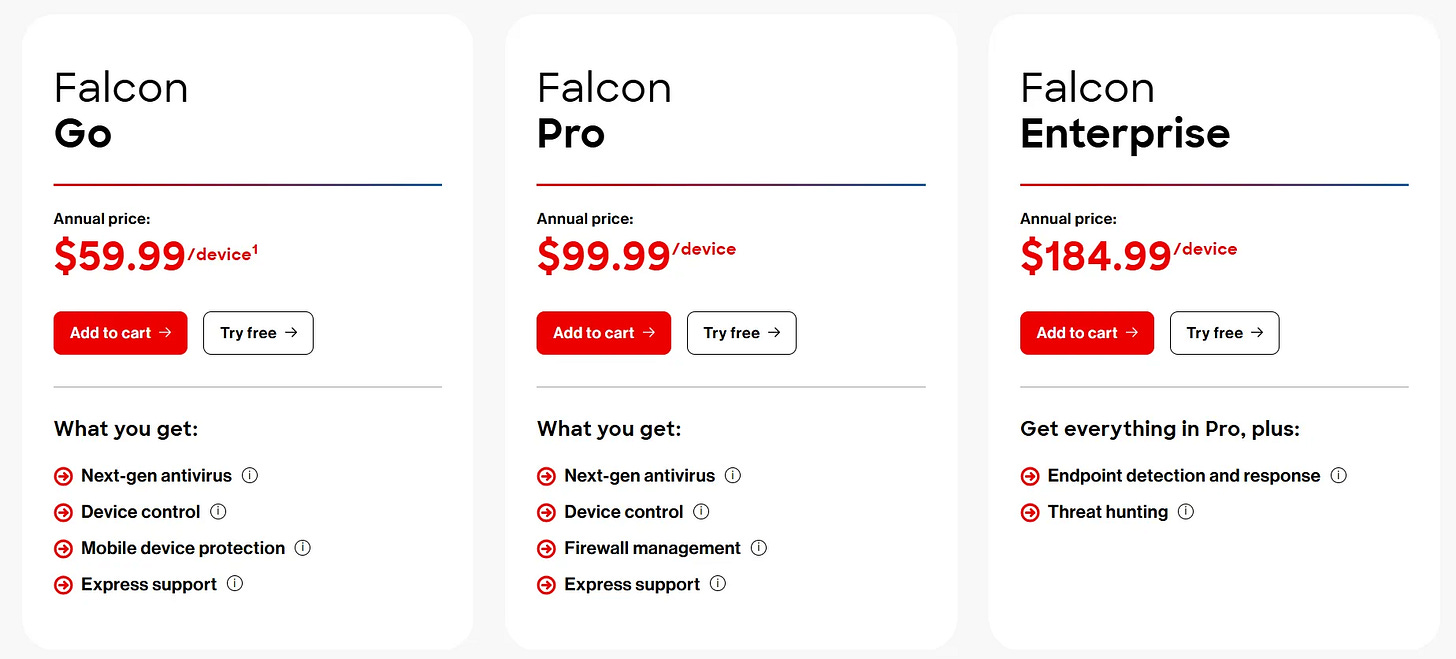
Need a specific example? Look at one of the most popular endpoint security products on the market today, Crowdstrike Falcon. A quick glance at their website shows that the first two Falcon tiers do not include EDR. You only get EDR when you go up to the Enterprise tier.
Today, AV and EDR are still separate codebases, executables, and products. Some vendors sell AV, but no EDR. Some sell EDR, but no AV. If we use the terms interchangeably, there is a very real chance that someone assumes they’re buying both, and ends up very disappointed1.
Optional History Lesson: NGAV
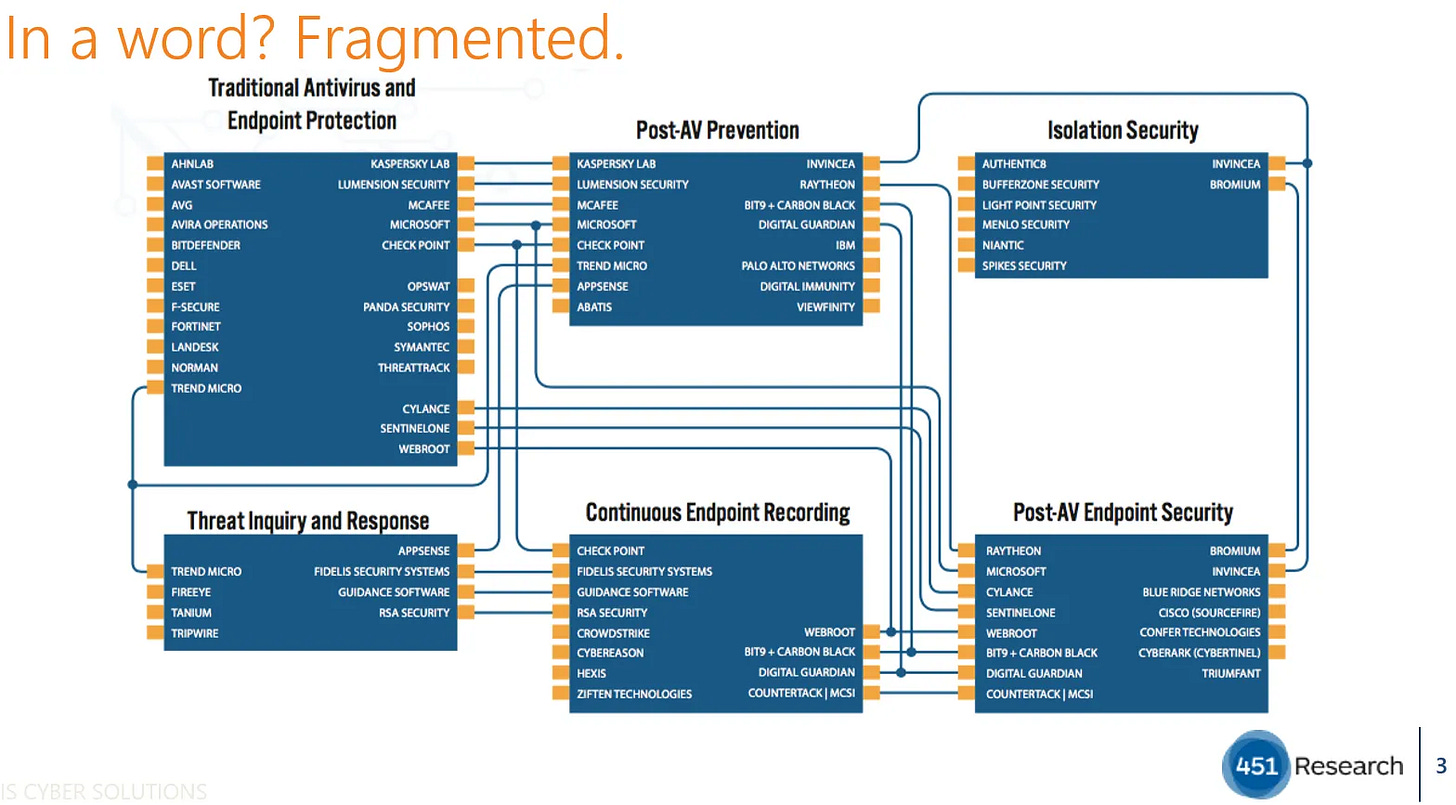
EDR and NGAV were born around the same time. The wave of endpoint security companies in the early 2010s that included Cybereason, Cylance, Crowdstrike, Carbon Black, Endgame, and others, zeroed in on one of two technologies:
a replacement for failing legacy AV approaches (”next-gen” AV)
real-time forensic collection of endpoint data (EDR)
Nobody did both initially, they chose one or the other. Over time, as they grew, most of the pure play endpoint security startups started offering both. I was lucky enough to be an analyst at 451 Research at the time, tracking over 100 endpoint security companies and talking to dozens of them every month to understand what was happening in this market. For the NGAV companies, the roadmap was clear:
prove out NGAV technology, and sell it alongside legacy AV (the complementary approach)
build out EPP functionality, so that NGAV can eventually displace legacy AV
build out EDR functionality (or if you were one of the companies that started with EDR, you needed to build NGAV, and then EPP)
Conquer and profit
The early days were interesting. It was obvious that the end goal was to topple the incumbents and begin competing with them, but none of these disruptors could admit to this out loud. They had to play nice for years, claiming to ‘complement’ legacy AV/EPP vendors. I dubbed it the curse of complementing. Endpoint disruption created a lot more than just NGAV and EDR - the market was much more fragmented in 2015.
You probably already know how this story played out. Symantec and McAfee liked to portray the image of highly diversified security platforms, but the reality was that their revenue was heavily dependent on the endpoint security market. The disruption happened quickly. I vividly recall Symantec’s SEP14 (Symantec Endpoint Protection, version 14) release. It was their attempt to catch up with the market, throwing all the new technologies that threatened to disrupt them into one major release. These new technologies were hastily bolted on, disabled by default, and buried deep in configuration screens. It was too little, too late.
While trying to catch up with the endpoint security competition, Symantec acquired Blue Coat (network security products), and Blue Coat’s exec team took over Symantec. Then Symantec also acquired LifeLock. To me, it seemed like they were trying to convince themselves that building a bigger suite of products would make their endpoint issues less critical to fix.
It did not. Rumor had it that they were bleeding out millions in revenue every quarter and the churn on renewals for endpoint products was particularly bad2. Almost exactly three years after Blue Coat’s execs took over, Symantec’s enterprise offerings were split out and sold off to Broadcom.
The impact to Symantec and McAfee was quick, decisive, and permanent. Before long, EDR and EPP were getting bundled together, and I believe this is when folks started conflating the terms, using “EDR” to refer to both.
Optional History Lesson: EDR
Why EDR though? What was driving it?
EDR was part of a shift in the industry, as we spotted some major gaps when it came to detecting attacks. When prevention failed, we lacked the forensic detail to figure out why it failed, how the malware got in, and what the malware/attacker did. The first EDR tools came out of shops with heavy incident response services3.
Shops like Mandiant had EDR-like tools, but you’d only run them once, after the attack was over and infected systems had been isolated. What if we had these tools running all the time? The IR folks wouldn’t be flying blind when investigating an attack and would be able to review telemetry from the time the bad thing happened.
In Conclusion: Why should you care?
You should care about the distinction between AV and EDR, because it will matter when your security program is placed under the post-breach microscope. Your cyber insurance provider will care. The FTC will care when writing up their complaint. The lawyers will care when assembling class-action lawsuits. Your customers and partners will care.
Or worse, someone ends up in a position where they told an auditor or regulator that AV was in use on systems, when they only had EDR installed.
Note that a lot of this information didn’t come directly from the vendors, so take them as rumors, not fact. They make sense though, given what was visibly happening to these vendors in the market.
Mandiant was one of the first to build the tooling here, but ironically, FireEye struggled to enter and compete in the endpoint security market. That’s another story for another time, though.