Breach Lessons: the 2023 MGM Breach
What really happened in the 2023 MGM breach
The MGM breach of 2023 is an interesting case study. Not only was this one of two breaches on casinos in September 2023 that unfolded very differently, but one of a string of attacks on Okta customers. The contrast between how MGM and Caesars handled their respective incidents tells two very different stories. While Caesars quietly paid a reported $15 million ransom1, MGM did not. For the next 10 days, MGM struggled with disruptions to their services and properties. Room cards not working, slot machines offline, staff using pen and paper to track orders and payouts. The loss of business during this time cost MGM an estimated $100 million. In the end, data from ~37 million people2 ended up on the dark web.
Before diving in, it is worth noting that this story has no neutral narrators. The attackers are incentivized to exaggerate their capabilities and downplay their collaboration with others, while MGM’s legal team is incentivized to minimize the perception of negligence. Where possible, this writeup relies on court filings, SEC disclosures, and third-party reporting, but some details inevitably trace back to sources with a stake in how the story is told.
Background
MGM Resorts International is one of the largest hospitality and entertainment companies in the world, operating over 30 hotel and casino destinations across the globe. With flagship properties like the Bellagio, Aria, and MGM Grand on the Las Vegas Strip, the company employs roughly 75,000 people, serves tens of millions of guests annually, and reported revenues of roughly $13 billion in 2022.

What were the circumstances around the attack?
The attack was made possible in large part by a misconfiguration in MGM's Okta environment. Okta is an identity and access management (IAM) platform that many large enterprises use to handle employee logins across dozens of applications through a single sign-on (SSO) system. Within Okta, Super Administrator accounts hold some of the highest privileges available, including the ability to link new Identity Providers (IdPs) and modify multi-factor authentication (MFA) policies.
On August 31st, 2023, over a week before the attack, Okta sent out a warning to all customers noting that attackers had been using social engineering to obtain privileged Okta roles, moving laterally from there. The notice included specific preventative measures and called the attack vector “preventable.” Whether MGM acted on that warning in time remains an open question. Critically, at the time of the breach, Okta’s default settings allowed lower-privilege help desk administrators to reset MFA for Super Admin accounts without any additional verification3.
In the months prior4, attackers had been systematically researching high-value organizations that use Okta. They identified employees with administrator-level privileges through public sources like LinkedIn, and used that information to manipulate help desk workers. MGM was one of several Okta customers targeted during this period.
Attacker Motive(s)
The attackers were financially motivated. While two groups have claimed responsibility (see Appendix B for more details on attribution) and both agree that ransomware and extortion were ultimately used, nearly every other detail of their stories diverge. An alleged Scattered Spider member told reporters that their original goal was to tamper with slot machines5 to slowly siphon funds via recruited mules. When that plan failed due to unfamiliarity with the source code, they shifted to ransomware. ALPHV denied any attempts to tamper with slot machines, arguing it would reduce the chances of a ransom payment. They further claimed to not have deployed ransomware until after MGM began taking down their own systems6.
Initial Point of Compromise
Getting an initial foothold into MGM came down to a short phone call. The attackers spent the early summer months conducting Open Source Intelligence (OSINT) on MGM through sources like LinkedIn. Eventually, they identified employees with administrator-level privileges and gathered enough details on their targets to stage a convincing social engineering attack. They called MGM’s help desk, impersonated one of those employees, and used the information gathered to back up their story. A brief conversation was enough to convince a help desk worker to reset MFA for a Super Administrator account.
From there, the attackers used this newfound Super Admin access to add an additional IdP inside the Okta environment. This feature, called Org2Org, is designed for company mergers where not all employees have been configured in Okta yet, allowing two separate Okta organizations to bridge their identity systems in the interim. By adding their own IdP, they could modify the username parameter to log in as any MGM user without needing to provide a password or undergo MFA. With just one click from their environment, they could impersonate anyone in the company.
This also gave the attackers a stealthy persistence mechanism that MGM inadvertently made worse for themselves. When MGM began to take down their Okta Sync Servers in order to lock out the attackers, they ended up only locking themselves out7. The attackers still retained Super Administrator access, letting them move laterally and disperse ransomware.
Impact
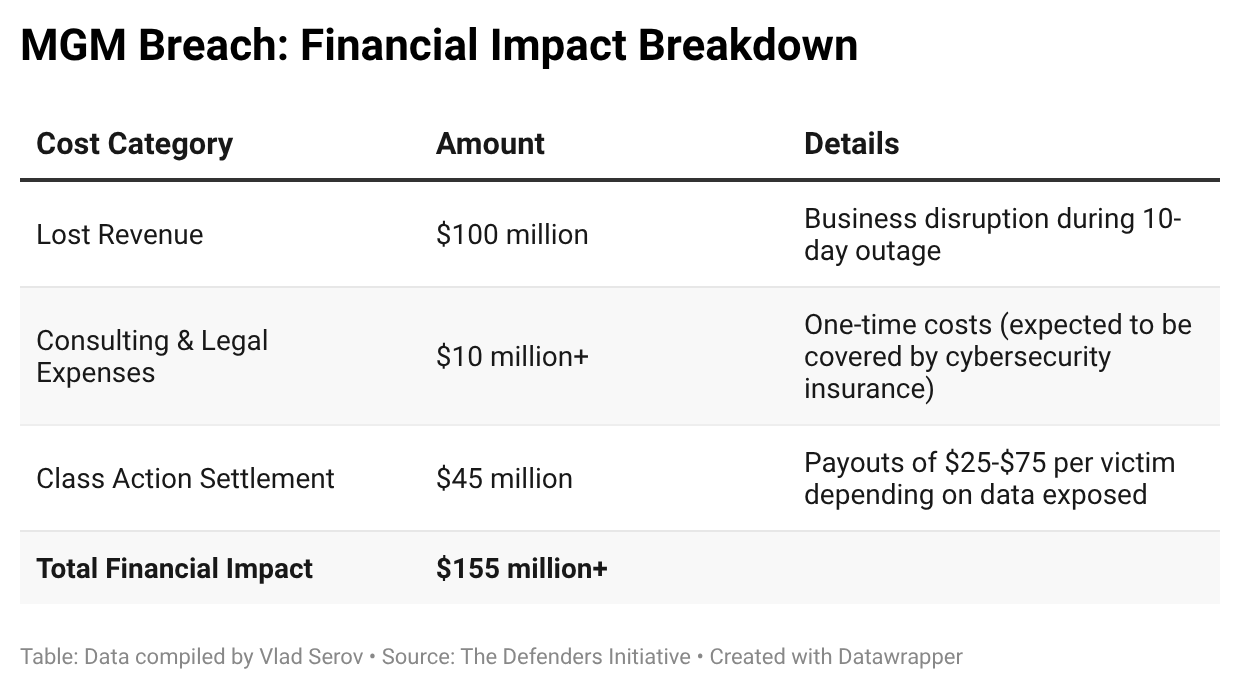
MGM’s decision not to pay the ransom was an expensive one. MGM’s operations are deeply dependent on digital infrastructure, from keycard systems and slot machines to hotel reservations and loyalty program data, making it an attractive target for a ransomware attack. The diversification of operations is also reflected in the categories of losses detailed in the table below.
The financial impact broke down as follows:
In addition, the data of roughly 37 million people ended up on the dark web, including names, contact information, dates of birth, and driver's license numbers, with Social Security and passport numbers exposed for a subset of victims. The FTC also issued a Civil Investigative Demand, which MGM responded to with a 71-page petition before it was eventually dropped8.
By comparison, Caesar’s reportedly paid a $15 million ransom in Bitcoin, but the FBI was later able to freeze approximately $11.8 million, limiting their loss to $3.2 million.
Legacy & Takeaways
MGM’s handling of the disclosure is worth noting. Their public communication was initially sparse, and the detailed 8-K filed with the SEC came nearly a month after the incident. While SEC disclosure requirements ensured some transparency, it was largely compelled rather than voluntary. Caesars, by contrast, managed to keep their breach almost entirely out of the public eye by paying quickly and quietly. Neither approach sets a great precedent. Timely, transparent disclosure gives affected customers the chance to protect themselves and gives the broader industry the information it needs to defend against similar attacks.
As for prevention, the attack did not require sophisticated malware or a zero-day exploit. It required online research and a phone call. Okta’s August 31st warning included specific, actionable steps that, if correctly implemented, could have stopped or slowed the attack at multiple stages. Limiting help desk admin roles to exclude highly privileged accounts would have opened this request to more scrutiny. Perhaps a more senior staff member would have spotted a request to reset MFA for a Super Admin as a red flag, stopping the attack before it began. Enabling Protected Actions would have forced re-authentication before any administrative action was taken, adding another layer the attackers would have had to bypass.
Whether the aftermath caught up with anyone actually responsible remains unclear. ALPHV’s dark web infrastructure was taken down in late 2023, and several alleged Scattered Spider members were subsequently arrested in 2024. However, given how murky the attribution remains, it is difficult to say with confidence that those charged were the same individuals who carried out the MGM breach specifically.
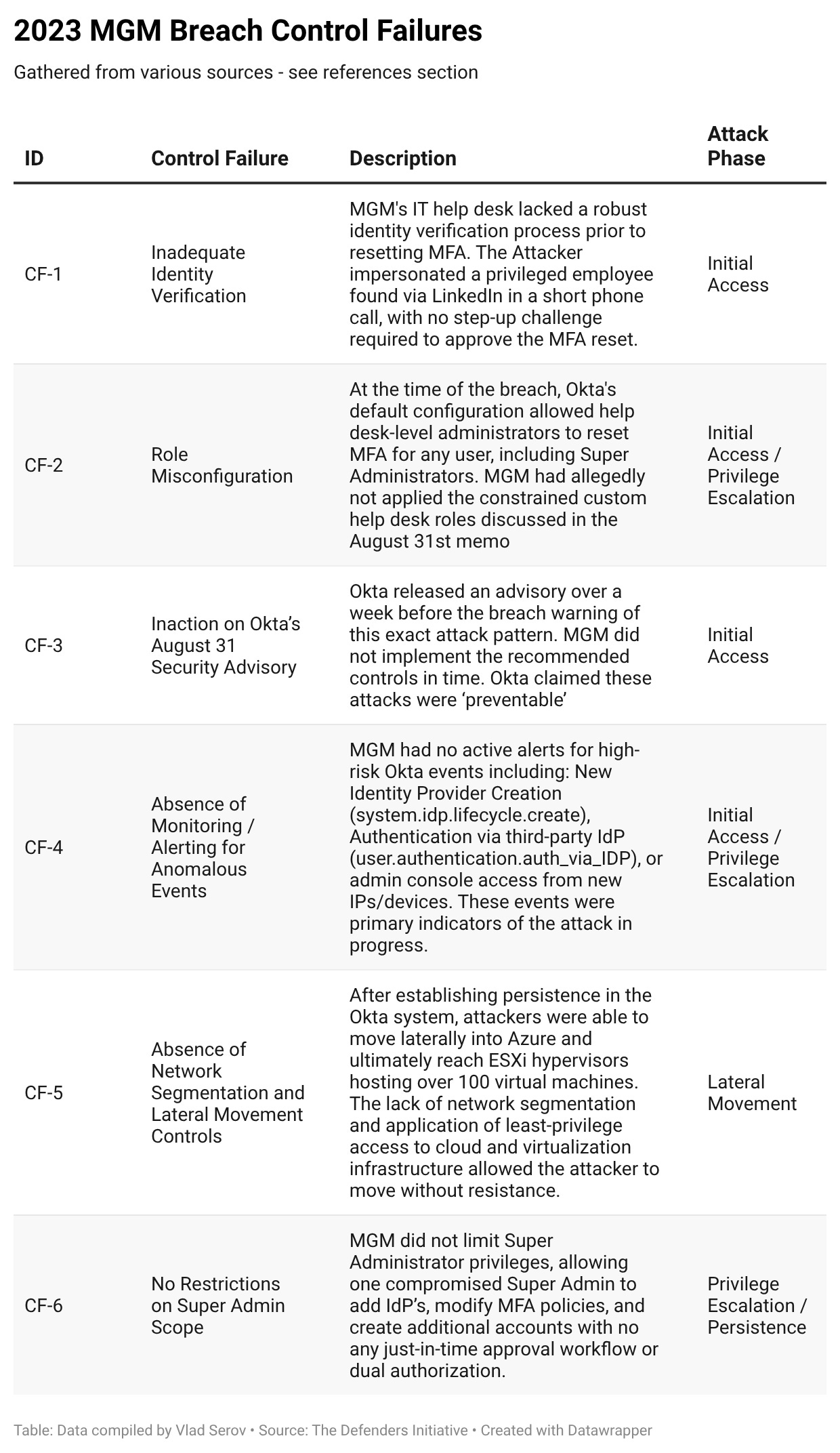
Appendix A: Control Failures
The following table details control failures from the MGM breach. For reference in other parts of the appendices, each control failure is assigned an ID, abbreviated as “CF-[number].” Control failures go beyond technical failures to include process and skill (people) failures as well.
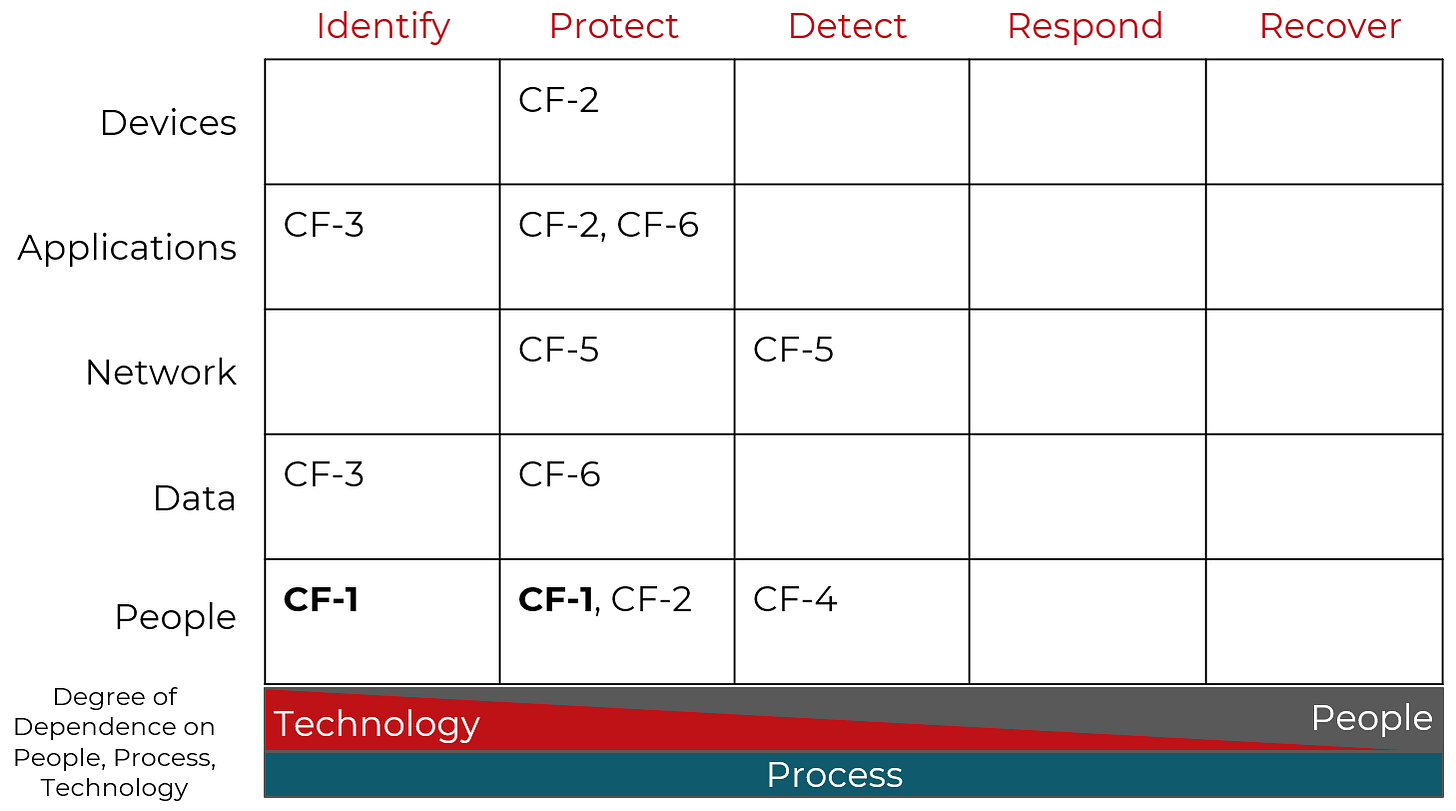
Cyber Defense Matrix Mapping
Using Sounil Yu’s Cyber Defense Matrix (CDM), which is based on NIST CSF functions and assets. Read more about the CDM here.
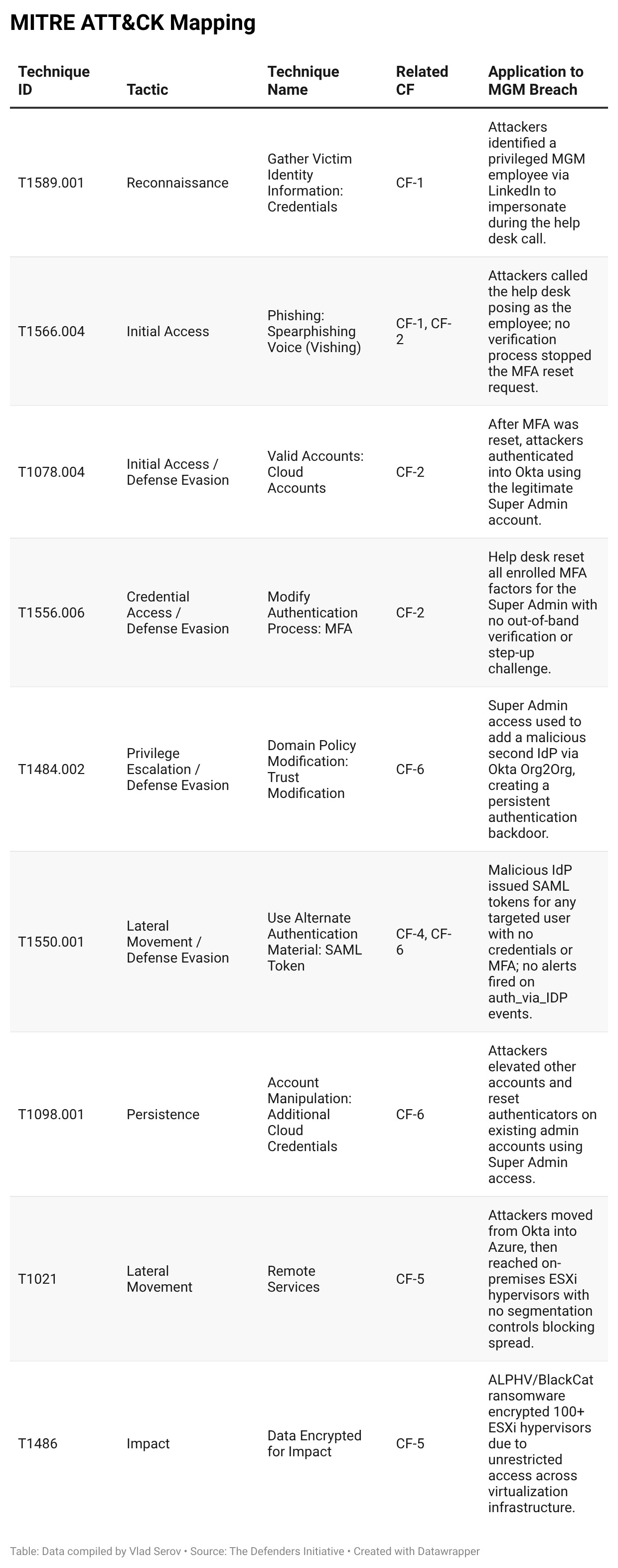
MITRE ATT&CK Mapping
This next table is for teams that depend on the MITRE ATT&CK matrix. These are the same control failures from the previous table, but reorganized from a MITRE ATT&CK techniques perspective.
ATT&CK Navigator Summary: Primary Tactics Leveraged
Reconnaissance ⇒ Initial Access ⇒ Credential Access ⇒ Privilege Escalation ⇒ Defense Evasion ⇒ Persistence ⇒ Lateral Movement ⇒ Impact
The attack is notable for its heavy use of Identity-based techniques (T1556, T1484, T1550) rather than common exploit-based initial access, highlighting the importance of identity infrastructure and its attack surface. Every tactic from Initial Access onward was enabled or amplified by the control failures in CF-1 through CF-4.
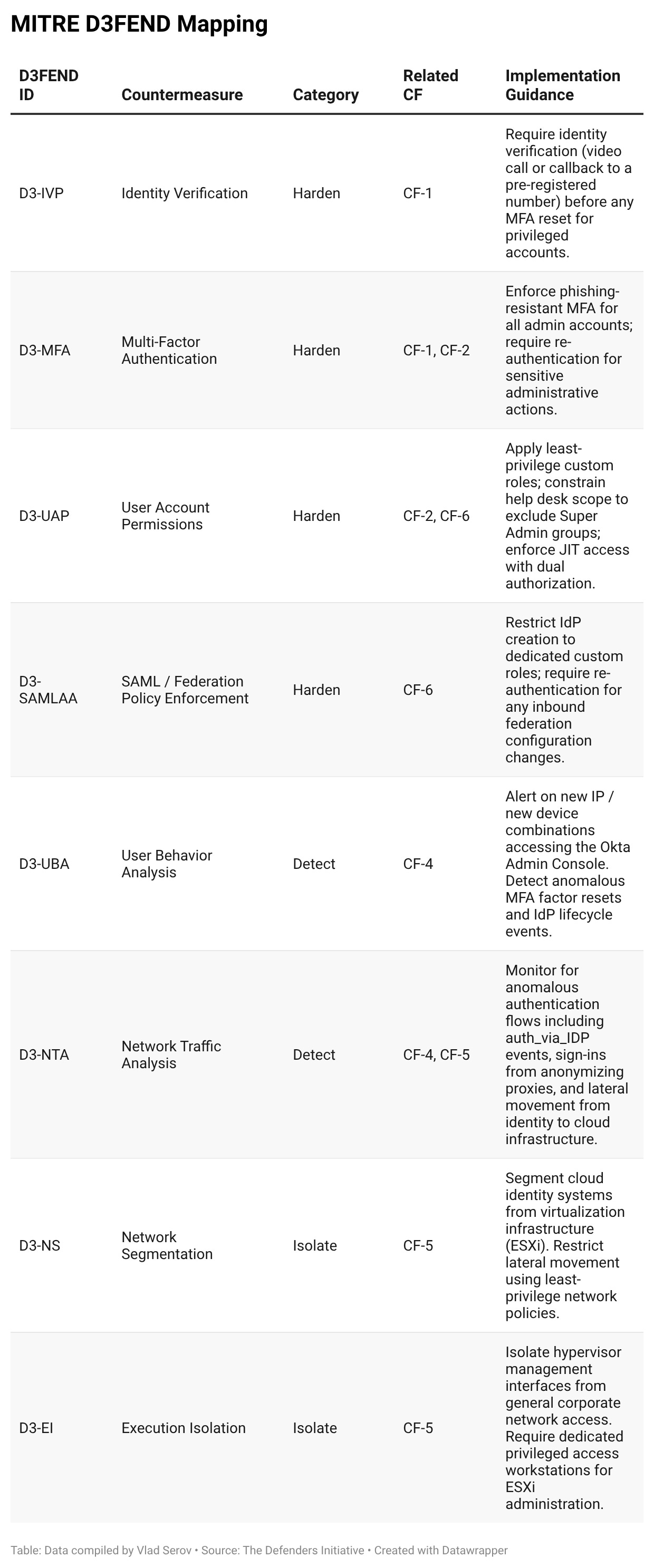
MITRE D3FEND Mapping
MITRE D3FEND mirrors the ATT&CK matrix. Where ATT&CK describes the techniques and tactics used by attackers, D3FEND describes the preventative and detective controls to ‘defend’ against them.
Appendix B: Attribution
Public reporting almost universally credited Scattered Spider with the MGM incident as well as incidents with other Okta customers. Scattered Spider is a loosely organized collective of young, English-speaking hackers known for aggressive social engineering. Security firms amplified the attribution, and the name stuck. But ALPHV/BlackCat, the ransomware group whose malware was ultimately deployed, published a lengthy statement on their dark web blog explicitly rejecting that framing. Scattered Spider, for their part, also claimed the operation as their own.
ALPHV’s statement is worth reading carefully. They not only claimed credit for the attack, they also pushed back against Scattered Spider being attributed. They called out VX Underground specifically for false reporting and challenged security firms to provide actual evidence of the perpetrators. In their own words, “these specialists find it difficult to delineate between the actions of various threat groupings, and so they simply grouped them together.” ALPHV also noted that tactics and indicators of compromise are publicly known and easy for anyone to imitate, meaning that pattern matching alone is not enough to pin an attack on a specific group.
ALPHV provides Ransomware as a Service (RaaS), which is why most sources attributed the attack to a collaborative effort between the two groups. Scattered Spider is known for gaining initial access via social engineering, then deploying ransomware purchased from other groups. In their statement, ALPHV seems to insult Scattered Spider, referring to them as “teenagers from the US and UK”, not something they would say if they were collaborating. With ALPHV’s data leak sites taken down in late 2023 and several alleged Scattered Spider members subsequently arrested, definitively attributing the MGM attack to either group remains impossible.
Appendix C: Timeline
August 31, 2023 - Okta sends out a warning to clients, stating that they have noticed attackers using social engineering to attain a privileged role in Okta, then laterally moving and escalating privileges. They specifically mentioned that these were “preventable and present several detection opportunities for defenders.”
September 8, 2023 - ALPHV Statement claims that they had access to MGM’s Okta this day. The attacker was able to socially engineer a help desk worker into resetting MFA for a Super Admin account, which was then accessed and used to add an additional IdP in Okta (a feature meant for companies undergoing a merger), this would allow them to sign in as MGM users using credentials from the IdP they added.
September 10, 2023 - First externally visible impacts from the attack - MGM started shutting down systems, impacting digital room keys, automated payouts for slot machines, website/reservation system outages, MGM app outages. Attackers claim that MGM began shutting systems down before any ransomware was used. According to the attackers, MGM began taking down all Okta Sync Servers, which allegedly locked MGM out of the Okta. Attackers were unaffected, and still had super admin privileges on Okta and access to MGM’s Azure.
September 11, 2023 - MGM announced on Twitter that it was dealing with a security incident. This is the day that over 100 ESXi hypervisors hosting many services MGM used were alleged to be encrypted with ransomware.
September 13, 2023 - The company projected it could lose up to $8.4M per day in revenue as issues continued. The company files a form 8-K (Legally required by the SEC to disclose any important information shareholders must know). Not much information is included
September 20 , 2023 - MGM confirms full restoration of services.
October 5, 2023 - MGM files another more in depth 8-K, in this form they disclosed that the “cyber incident” negatively impacted them by $100M, and “less than $10(M) in one-time expenses in the third quarter related to the cybersecurity issue, which consisted of technology consulting services, legal fees and expenses of other third party advisors. Although the Company currently believes that its cybersecurity insurance will be sufficient to cover the financial impact to its business as a result of the operational disruptions, the one-time expenses described above and future expenses, the full scope of the costs and related impacts of this issue has not been determined.” They believed the scope of the breach to be limited to “personal information (including name, contact information (such as phone number, email address and postal address), gender, date of birth and driver’s license numbers).” as well as SSN and passport numbers for some. They claimed that no payment information was leaked.
October 26, 2023 - MGM releases a statement that some Canadian customers were impacted, and sent an email to affected individuals with more information.
December 19, 2023 - ALPHV’s data leak sites are taken down by the FBI, and a decryption tool is sent to victims.
January 25, 2024 - FTC Staff issued a Civil Investigative Demand (“CID”) to MGM seeking large quantities of documents and information.
February 20, 2024 - MGM files a 71 page Petition, this document argues that the FTC is overreaching in their requests. Much of the correspondence between MGM and the FTC is redacted. The CID is later dropped.
March 22, 2024 - Class action lawsuits are consolidated into one lawsuit: Tanya Owens, et al. vs. MGM Resorts International, et al. They will then further combine with a class action group from the 2019 data breach on MGM in July of 2023.
October 31, 2024 - A settlement is reached with MGM, requiring them to pay $45M total, $75 to a victim who had their SSN or Military ID leaked, $50 to anyone who had a passport number or DL number leaked, and $25 to anyone who had their name, address, and DoB leaked. Additional money would be paid out to victims of identity theft on a case by case basis.
January 17, 2025 - After more negotiations, the parties enter a Settlement Agreement, which would then be put up to a vote for all affected members.
February - April 2025 - Notices are sent out to victims, who have until June 18, 2025 to claim their money
June 18, 2025 - Settlement period is complete and the website is taken down
Appendix D: References
Breach Info
https://www.wsj.com/business/hospitality/caesars-paid-ransom-after-suffering-cyberattack-7792c7f0
https://blog.checkpoint.com/security/cyber-stakes-the-mgm-ransomware-roulette/
https://techcrunch.com/2023/09/14/mgm-cyberattack-outage-scattered-spider/
https://www.forbes.com/sites/steveweisman/2025/03/12/mgm-ransomware--attack-update/
https://www.ft.com/content/a25d2897-b0ce-4ba7-92ed-ff5df09d1b47
Threat Intelligence/Writeups
https://cybersecurity.fullcoll.edu/wp-content/uploads/sites/69/2025/05/MGM-Writeup.pdf
https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-320a
https://wing.security/saas-security/a-saas-misconfiguration-case-study/
Govt Sources
https://www.sec.gov/Archives/edgar/data/789570/000119312523251667/d461062d8k.htm
https://d18rn0p25nwr6d.cloudfront.net/CIK-0000789570/a390c443-0c40-4025-aba2-74505ab3c9e3.pdf
https://www.ftc.gov/system/files/ftc_gov/pdf/2423028mgmpetquashpublic.pdf
Settlement Info
https://web.archive.org/web/20250506152518/https://mgmdatasettlement.com/
https://cases.justia.com/federal/district-courts/nevada/nvdce/2:2023cv01480/164564/98/0.pdf
Okta Info
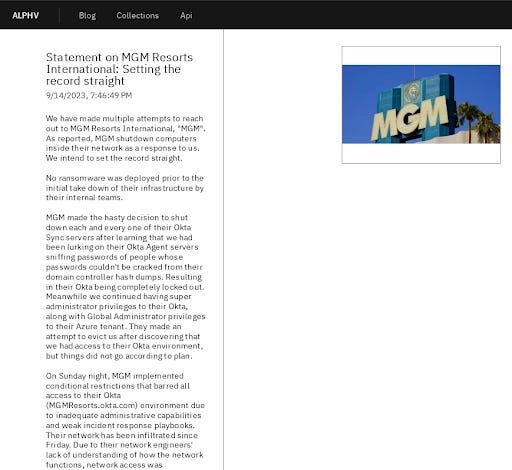
Appendix E: ALPHV Statement
Disclaimer: The statement reproduced below is attributed to ALPHV/BlackCat based on coverage from reputable cybersecurity outlets including BleepingComputer, Malwarebytes, and Check Point, all of whom reported on its publication to ALPHV's dark web leak site on September 14, 2023. We cannot independently verify that this represents the complete and unaltered text of the original statement, as the primary source was taken down by the FBI in December 2023 and is no longer accessible.
We have made multiple attempts to reach out to MGM Resorts International, “MGM”. As reported, MGM shutdown computers inside their network as a response to us. We intend to set the record straight.
No ransomware was deployed prior to the initial take down of their infrastructure by their internal teams.
MGM made the hasty decision to shut down each and every one of their Okta Sync servers after learning that we had been lurking on their Okta Agent servers sniffing passwords of people whose passwords couldn’t be cracked from their domain controller hash dumps. Resulting in their Okta being completely locked out. Meanwhile we continued having super administrator privileges to their Okta, along with Global Administrator privileges to their Azure tenant. They made an attempt to evict us after discovering that we had access to their Okta environment, but things did not go according to plan.
On Sunday night, MGM implemented conditional restrictions that barred all access to their Okta (MGMResorts.okta.com) environment due to inadequate administrative capabilities and weak incident response playbooks. Their network has been infiltrated since Friday. Due to their network engineers’ lack of understanding of how the network functions, network access was problematic on Saturday. They then made the decision to “take offline” seemingly important components of their infrastructure on Sunday.
After waiting a day, we successfully launched ransomware attacks against more than 100 ESXi hypervisors in their environment on September 11th after trying to get in touch but failing. This was after they brought in external firms for assistance in containing the incident.
In our MGM victim chat, a user suddenly surfaced a few hours after the ransomware was deployed. As they were not responding to our emails with the special link provided (In order to prevent other IT Personnel from reading the chats) we could not actively identify if the user in the victim chat was authorized by MGM Leadership to be present.
We posted a link to download any and all exfiltrated materials up until September 12th, on September 13th in the same discussion. Since the individual in the conversation did not originate from the email but rather from the hypervisor note, as was already indicated, we were unable to confirm whether they had permission to be there.
To guard against any unneeded data leaking, we added a password to the data link we provided them. Two passwords belonging to senior executives were combined to create the password. Which was clearly hinted to them with asterisks on the bulk of the password characters so that the authorized individuals would be able to view the files. The employee ids were also provided for the two users for identification purposes.
The user has consistently been coming into the chat room every several hours, remaining for a few hours, and then leaving. About seven hours ago, we informed the chat user that if they do not respond by 11:59 PM Eastern Standard Time, we will post a statement. Even after the deadline passed, they continued to visit without responding. We are unsure if this activity is automated but would likely assume it is a human checking it.
We are unable to reveal if PII information has been exfiltrated at this time. If we are unable to reach an agreement with MGM and we are able to establish that there is PII information contained in the exfiltrated data, we will take the first steps of notifying Troy Hunt from HaveIBeenPwned.com. He is free to disclose it in a responsible manner if he so chooses.
We believe MGM will not agree to a deal with us. Simply observe their insider trading behavior. You believe that this company is concerned for your privacy and well-being while visiting one of their resorts?
We are not sure about anyone else, but it is evident from this that no insiders have purchased any stock in the past 12 months, while 7 insiders have sold shares for a combined 33 MILLION dollars (https://www.marketbeat.com/stocks/NYSE/MGM/insider-trades/). This corporation is riddled with greed, incompetence, and corruption.
We recognize that MGM is mistreating the hotel’s customers and really regret that it has taken them five years to get their act together. Other lodging options, including casinos, are undoubtedly open and happy to assist you.
At this point, we have no choice but to criticize VX Underground for falsely reporting events that never happened. We typically consider their information to be highly reliable and timely, but we did not attempt to tamper with MGM’s slot machines to spit out money because doing so would not be to our benefit and would decrease the chances of any sort of deal.
The rumors about teenagers from the US and UK breaking into this organization are still just that—rumors. We are waiting for these ostensibly respected cybersecurity firms who continue to make this claim to start providing solid evidence to support it. Starting to the actors’ identities as they are so well-versed in them.
The truth is that these specialists find it difficult to delineate between the actions of various threat groupings, therefore they have grouped them together. Two wrongs do not make a right, thus they chose to make false attribution claims and then leak them to the press when they are still unable to confirm attribution with high degrees of certainty after doing this. The tactics, procedures, and indicators of compromise (TTPs) used by the people they blame for the attacks are known to the public and are relatively easy for anyone to imitate.
The ALPHV ransomware group has not before privately or publicly claimed responsibility for an attack before this point. Rumors were leaked from MGM Resorts International by unhappy employees or outside cybersecurity experts prior to this disclosure. Based on unverified disclosures, news outlets made the decision to falsely claim that we had claimed responsibility for the attack before we had.
We still continue to have access to some of MGM’s infrastructure. If a deal is not reached, we shall carry out additional attacks. We continue to wait for MGM to grow a pair and reach out as they have clearly demonstrated that they know where to contact us.
Caesars has not publicly confirmed the exact amount. The $15 million figure comes from reporting by the Wall Street Journal as well as court documents thought to be attributed to the payment alleged to have been made by Caesars. These documents also suggest that roughly two-thirds of the ransom were recovered.
The $37 million figure comes from reporting and is reflected in the consolidated class action complaint.
This default behavior is documented in an Okta support thread predating the breach.
The specific timeframe of the reconnaissance period is not established in MGM's SEC disclosures or the Okta advisory. This framing reflects reporting and attacker accounts rather than a verified primary source.
The slot machine tampering account was reported by the Financial Times based on statements from a purported Scattered Spider member speaking to journalists directly. ALPHV denied this version of events entirely in their own statement. Neither account has been corroborated by court filings or law enforcement disclosures available at the time of writing.
Please see Appendix E for more information
This sequence of events originates entirely from ALPHV's statement. MGM has not publicly confirmed or denied this specific claim. It should be read as the attacker's account, not an established fact.